The main problem with Telnet/rsh/rlogin/rcp is that they send the information over the wire unencrypted. So whatever you type, your username/passwords that go in clear text over the wire. Anybody can sniff it and make your life difficult. The remote shell utilities such as, rsh, depend on a pre authenticated IP connection. Anything coming from that IP is reliable for them. IP spoofing is not difficult!
So use SSH, Secure way to send information over network.The Secure Shell keeps unauthorized users out of our computers, both by encrypting passwords to protect them from sniffing, and by providing more positive authentication than simple password exchange. Instead of rsh, rcp, and rlogin, simply use the commands ssh, scp, or slogin.
How to tunnel Telnet through SSH:
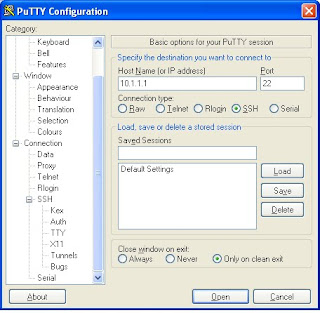
1. Launch Putty and provide the destination host IP address.
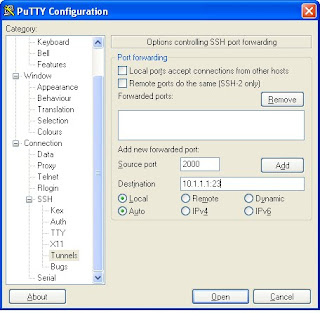
 2. Go to SSH->Tunnel.Enter the destination server name or address followed by a colon and the port PuTTY will forward to.
2. Go to SSH->Tunnel.Enter the destination server name or address followed by a colon and the port PuTTY will forward to.
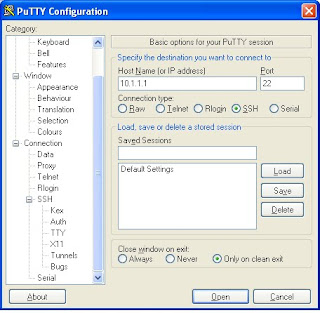
3.Click on the Open button. A terminal window will and prompt you to logon to the remote host using SSH. Enter your name and password to login to the remote host.
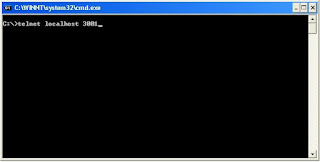
 4.Now you can connect to this server using any non secure Telnet client. You must note here that you have to connect to the same port which is specified for the destination server in step 2.
4.Now you can connect to this server using any non secure Telnet client. You must note here that you have to connect to the same port which is specified for the destination server in step 2.
So use SSH, Secure way to send information over network.The Secure Shell keeps unauthorized users out of our computers, both by encrypting passwords to protect them from sniffing, and by providing more positive authentication than simple password exchange. Instead of rsh, rcp, and rlogin, simply use the commands ssh, scp, or slogin.
How to tunnel Telnet through SSH:
1. Launch Putty and provide the destination host IP address.
 2. Go to SSH->Tunnel.Enter the destination server name or address followed by a colon and the port PuTTY will forward to.
2. Go to SSH->Tunnel.Enter the destination server name or address followed by a colon and the port PuTTY will forward to.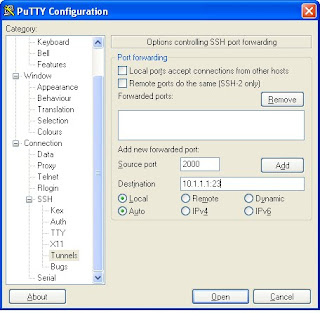
3.Click on the Open button. A terminal window will and prompt you to logon to the remote host using SSH. Enter your name and password to login to the remote host.
 4.Now you can connect to this server using any non secure Telnet client. You must note here that you have to connect to the same port which is specified for the destination server in step 2.
4.Now you can connect to this server using any non secure Telnet client. You must note here that you have to connect to the same port which is specified for the destination server in step 2.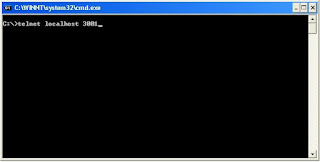
Comments
At the command prompt (cygwin or bash)
# ssh -L 3001:localhost:23 user@domain.com
If you've gone through the trouble of creating a key pair you can get avoid having to enter the password each time you set up the tunnel.
SSH tunneling is even more useful as a tool to bypass restrictive proxies. If you use dynamic tunneling, you can effectively create a SOCKS proxy. For example if you did this:
# ssh -D 8080 user@domain.com
You can now set up your browser to use localhost:8080 as a SOCKS proxy, allowing you to tunnel everything through it. For maximum security you can enable remote DNS lookups in your browser(Firefox has this setting under about:config) so that your browser does not use the default DNS server for name lookups.