NetBIOS an acronym for Network Basic Input/Output System. It provides services related to the session layer of the OSI model allowing applications on separate computers to communicate over a local area network. As strictly an API, NetBIOS is not a networking protocol. [Reference:http://en.wikipedia.org/wiki/NetBIOS]
Risks of NetBIOS:
1)NetBIOS Null Session Enabled: A NetBIOS null session allows users to connect to a host remotely with no username and password and perform a limited set of administrative tasks. Null sessions allow the remote user to gather information such as:
1. List users
2. List groups
3. List shares (including hidden shares)
4. Policies (such as minimum password length, etc.) While the enumerated information is not an immediate risk, much of the information can be leveraged to launch an attack to gain user or administrative privilege. All steps should be taken to eliminate the vulnerability and/or reduce the information available to the attacker.
2)NBTSTAT : All Microsoft Windows platforms include support for the NetBIOS network protocol stack. The NetBIOS protocol provides the underlying support for Microsoft Windows file and resource sharing. One component of all Microsoft Windows NetBIOS implementations is the NetBIOS Name Service. The NetBIOS Name Service listens for name service requests on UDP port 137. It can be queried to retrieve a listing of currently logged in user accounts and groups. In addition, the MAC address for the network interface over which the query is performed is included in the response to a nbtstat -A request.
The DOS nbtstat command can be used to perform this operation.
To do so, open a DOS command prompt and run the following command: nbtstat -A target_system Where target_system is the IP address or hostname of the target system.
See the picture below:
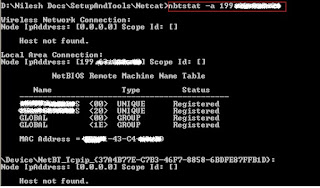
It shows that the Sharing is enabled on the target machine-see the code <20>. The attacker can now use other similar commands to get access to the shared resource:
net view \\target-ip
 It will list down all the shared resources on the remote machine. Now you can map them to your own disk:
It will list down all the shared resources on the remote machine. Now you can map them to your own disk:
net use K: \\target-ip\shared-resource-name
 Now the shared resource on the remote machine is shared on your machine with Drive letter K:
Now the shared resource on the remote machine is shared on your machine with Drive letter K:
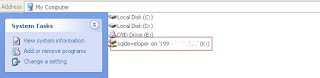
The content of the shared resource is available to you. You can browse them as they are on your own computer. As the NetBIOS is not a big issue on LAN, it may be big risk if your PC is connected over WAN.
Blocking NetBIOS on the system can be done one of three ways: [Reference: Cisco.com]
1) Use a network router upstream from the affected system to block TCP port 139 and port 445 to your network.
2) Use a software firewall on the affected system and block TCP port 139 and TCP port 445.
3) Disable 'WINS TCP/IP Client' bindings in Windows NT or Windows 2000.
How to disable NetBIOS:
To disable NetBIOS in Windows XP:
a)Click ‘Start’ from the Start Menu
b)Go to ‘Control Panel’
c)Go to ‘Network Connections’
d)Click on the interface for you wish to disable Netbios
e) Select Internet Protocol (TCP/IP) and then the Properties button.
f) Now select the Advanced button.
g) Then click on the WINS tab.
h) From there, click Disable NetBIOS over TCP/IP.
i) Click Ok 2 times after you've finished making your changes and restart as requested.
To disable NetBIOS in Windows 2000:
a) Click 'Start' from the Start Menu
b) Click 'Settings'
c) Click 'Network and Dialup Connections'
d) Click on the interface for you wish to disable Netbios
e) Select the 'Internet Protocol (TCP/IP) component
f) Select 'Properties'
g) Click the 'Advanced' button
h) Select the 'WINS' tab
i) Click 'Disable Netbios over TCP/IP'
j) Click 'OK'
To disable NetBIOS in Windows NT 4.0:
a) Click 'Start' from the Start Menu
b) Click 'Settings'
c) Click 'Control Panel'
d) Double click on 'Network'
e) Click on the Bindings tab
f) Under 'Show Bindings for:' select 'all adapters'
g) Find the network card you wish to disable Netbios for and expand it
h) Select 'WINS Client (TCP/IP)', and hit the 'Disable' button
I) Then reboot for the change to take effect
Risks of NetBIOS:
1)NetBIOS Null Session Enabled: A NetBIOS null session allows users to connect to a host remotely with no username and password and perform a limited set of administrative tasks. Null sessions allow the remote user to gather information such as:
1. List users
2. List groups
3. List shares (including hidden shares)
4. Policies (such as minimum password length, etc.) While the enumerated information is not an immediate risk, much of the information can be leveraged to launch an attack to gain user or administrative privilege. All steps should be taken to eliminate the vulnerability and/or reduce the information available to the attacker.
2)NBTSTAT : All Microsoft Windows platforms include support for the NetBIOS network protocol stack. The NetBIOS protocol provides the underlying support for Microsoft Windows file and resource sharing. One component of all Microsoft Windows NetBIOS implementations is the NetBIOS Name Service. The NetBIOS Name Service listens for name service requests on UDP port 137. It can be queried to retrieve a listing of currently logged in user accounts and groups. In addition, the MAC address for the network interface over which the query is performed is included in the response to a nbtstat -A request.
The DOS nbtstat command can be used to perform this operation.
To do so, open a DOS command prompt and run the following command: nbtstat -A target_system Where target_system is the IP address or hostname of the target system.
See the picture below:
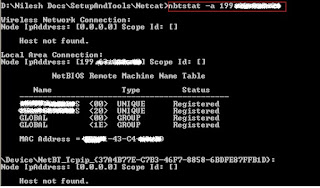
It shows that the Sharing is enabled on the target machine-see the code <20>. The attacker can now use other similar commands to get access to the shared resource:
net view \\
 It will list down all the shared resources on the remote machine. Now you can map them to your own disk:
It will list down all the shared resources on the remote machine. Now you can map them to your own disk:net use K: \\target-ip\shared-resource-name
 Now the shared resource on the remote machine is shared on your machine with Drive letter K:
Now the shared resource on the remote machine is shared on your machine with Drive letter K: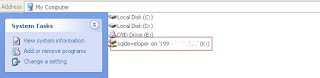
The content of the shared resource is available to you. You can browse them as they are on your own computer. As the NetBIOS is not a big issue on LAN, it may be big risk if your PC is connected over WAN.
Blocking NetBIOS on the system can be done one of three ways: [Reference: Cisco.com]
1) Use a network router upstream from the affected system to block TCP port 139 and port 445 to your network.
2) Use a software firewall on the affected system and block TCP port 139 and TCP port 445.
3) Disable 'WINS TCP/IP Client' bindings in Windows NT or Windows 2000.
How to disable NetBIOS:
To disable NetBIOS in Windows XP:
a)Click ‘Start’ from the Start Menu
b)Go to ‘Control Panel’
c)Go to ‘Network Connections’
d)Click on the interface for you wish to disable Netbios
e) Select Internet Protocol (TCP/IP) and then the Properties button.
f) Now select the Advanced button.
g) Then click on the WINS tab.
h) From there, click Disable NetBIOS over TCP/IP.
i) Click Ok 2 times after you've finished making your changes and restart as requested.
To disable NetBIOS in Windows 2000:
a) Click 'Start' from the Start Menu
b) Click 'Settings'
c) Click 'Network and Dialup Connections'
d) Click on the interface for you wish to disable Netbios
e) Select the 'Internet Protocol (TCP/IP) component
f) Select 'Properties'
g) Click the 'Advanced' button
h) Select the 'WINS' tab
i) Click 'Disable Netbios over TCP/IP'
j) Click 'OK'
To disable NetBIOS in Windows NT 4.0:
a) Click 'Start' from the Start Menu
b) Click 'Settings'
c) Click 'Control Panel'
d) Double click on 'Network'
e) Click on the Bindings tab
f) Under 'Show Bindings for:' select 'all adapters'
g) Find the network card you wish to disable Netbios for and expand it
h) Select 'WINS Client (TCP/IP)', and hit the 'Disable' button
I) Then reboot for the change to take effect
Comments